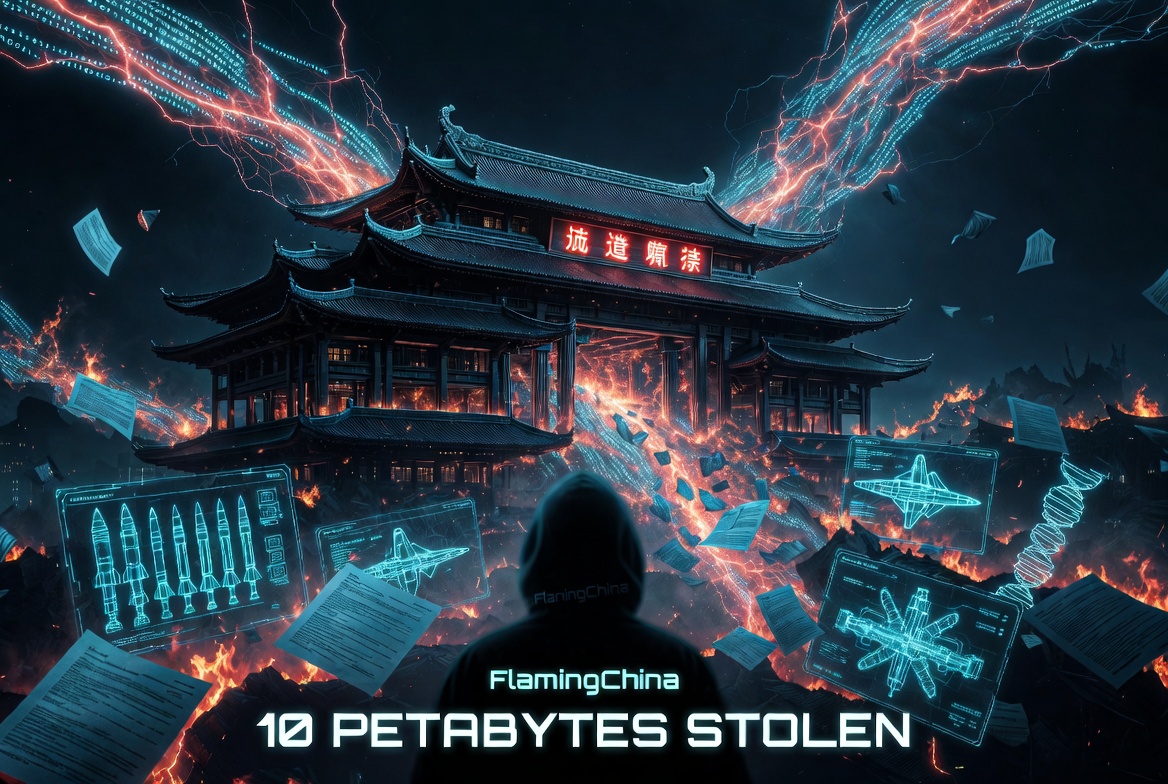
Massive Cyber Breach at China’s National Supercomputing Center: 10 Petabytes of Sensitive Military and Scientific Data Allegedly Stolen
In a major cybersecurity incident that has captured global attention, hackers claim to have infiltrated one of China’s premier supercomputing facilities and exfiltrated a staggering 10 petabytes of highly sensitive data.
The breach, first highlighted by the news aggregator Visegrád 24 on X (formerly Twitter) and covered by outlets including CNN, targets the National Supercomputing Center (NSCC) in Tianjin — a critical hub supporting advanced research for thousands of clients, including defense agencies, universities, and state-owned enterprises.
The Scale of the Alleged Heist
To understand the magnitude: 10 petabytes equals roughly 10 million gigabytes — enough data to store decades of high-resolution simulations, blueprints, and research archives. According to the hackers, who operate under the handle “FlamingChina,” the stolen materials include:
- Missile and bomb schematics
- Aerospace and aviation research
- Bioinformatics datasets
- Nuclear fusion simulation models
- Other classified military and defense documents
The group first posted samples of the data on an anonymous Telegram channel on February 6, 2026, and has since been offering the full dataset for sale via cryptocurrency on dark web forums and through direct outreach to cybersecurity researchers.
Experts who reviewed the leaked samples told CNN the data appears genuine, though independent verification of the entire 10-petabyte archive remains limited. The intrusion reportedly lasted several months, with data quietly siphoned out after initial access was gained through a compromised VPN or similar entry point.
How the Breach Reportedly Went Undetected for MonthsThe NSCC in Tianjin is no ordinary data center — it powers some of China’s most advanced scientific and military simulations. Yet the hackers claim they operated inside the system for around six months without triggering alarms. This prolonged undetected presence points to potential weaknesses in monitoring, access controls, or human factors — a vulnerability that has fueled widespread online commentary.
Many observers have noted the irony: China, frequently accused of large-scale intellectual property theft and cyber espionage against Western targets, now finds itself on the defensive in what could be one of the largest known data exfiltrations from its critical infrastructure.
Geopolitical Fallout and Broader Implications
If confirmed, this breach represents far more than a technical failure. It could expose years of cutting-edge work in hypersonics, next-generation fighters, missile technology, and fusion energy research. The data’s potential proliferation raises serious national security concerns for Beijing — and equally intriguing possibilities for rival intelligence services.
Social media reactions have been swift and pointed.
Comments range from schadenfreude (“China gets a taste of its own medicine”) to speculation about state involvement (“Bet Israel did it” or calls for the U.S. to acquire the dataset). Others highlight the strategic disaster: months of undetected access signals a major breakdown in China’s supposedly robust cyber defenses.
As of April 9, 2026, Chinese authorities have remained silent on the matter — consistent with their typical approach to such incidents.
What This Means for Cybersecurity in 2026
This story is still developing, but it already serves as a sobering reminder: even the most fortified national computing infrastructure can be compromised. In an era of escalating cyber tensions between major powers, the FlamingChina breach underscores how vulnerable critical research hubs remain — regardless of geography or claimed technological superiority.
For governments, enterprises, and researchers worldwide, the incident highlights the urgent need for stronger zero-trust architectures, continuous monitoring, and rapid incident response. It also raises uncomfortable questions about the future of data as a strategic asset: once exfiltrated and offered for sale, sensitive research can end up anywhere.
Stay tuned. In the shadowy world of cyber espionage, today’s breach could reshape tomorrow’s balance of power. If the full dataset surfaces publicly or falls into state hands, the ripple effects could be felt for years.
Sources: Visegrád 24 reporting, CNN coverage, and independent cybersecurity analyses. This post is based on publicly available claims and expert assessments as of April 9, 2026.
BREAKING:
— Visegrád 24 (@visegrad24) April 9, 2026
Hackers have stolen 10 petabytes of data from China’s largest state-run supercomputing facility in Tianjin
The hackers were inside the system for months & stole:
– Missile and bomb schematics
– Aerospace and aviation research
– Bioinformatics & fusion simulation data pic.twitter.com/TJY4J2QzNx
Leave a Reply
You must be logged in to post a comment.